See the invoice. Attributed to the work.
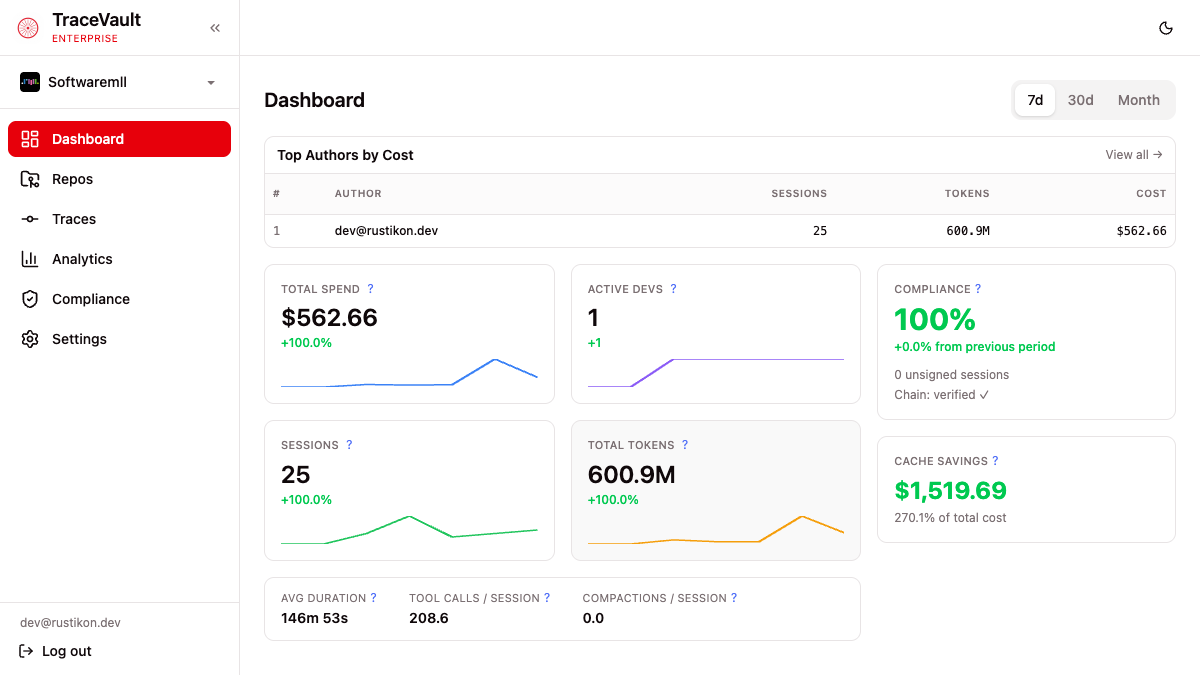
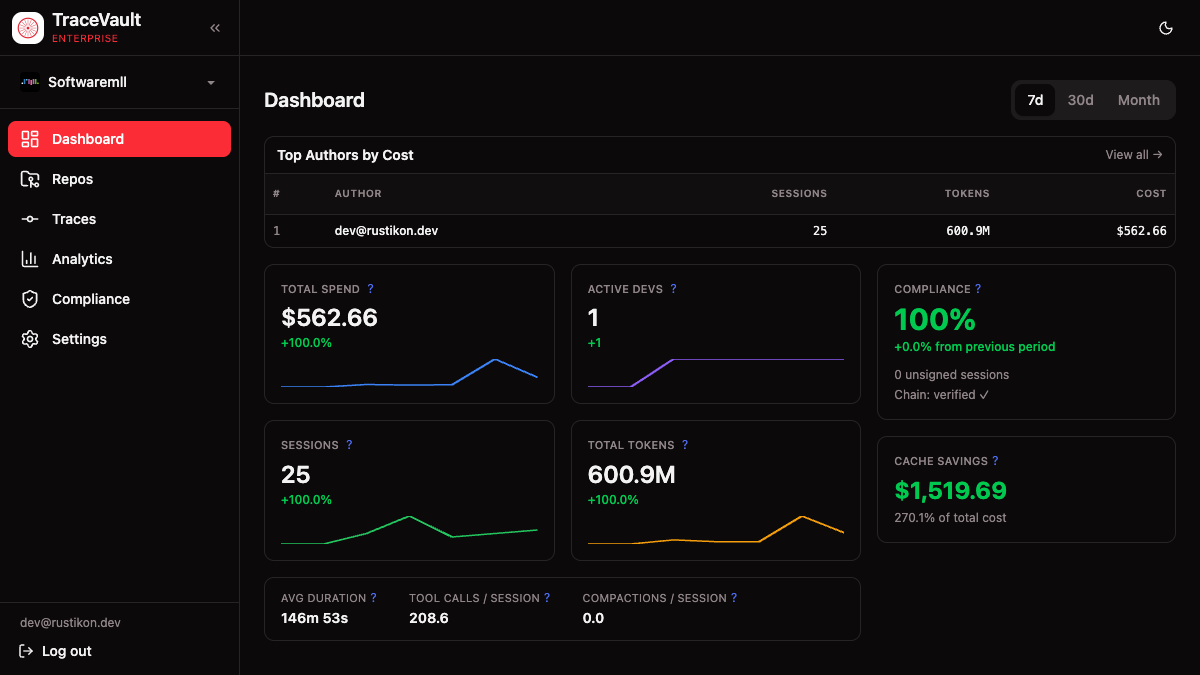
The same ledger that proves what AI did also answers how much it cost, which model burned the tokens and which team, repo or PR the spend belongs to.
- Token usage trends Daily and weekly consumption, broken out by model, team and repo — not a single monthly number.
- Cost tracking Spend attributed to session, author and PR, reconciled against vendor pricing as it changes.
- Cache savings Hit-rate per model and per project — surface the prompts that are quietly doubling the bill.
- Model distribution Which models the org actually uses. Side-by-side with the allowlist, so drift is visible.
- Team & author activity Adoption and throughput per team, with attribution by author — not a seat count.
- AI share of code Git-integrated, line-level overlay: exactly what AI wrote, where it landed, in which commits.
Community: basic traces + policy engine. Enterprise: full dashboard & reports.